How Zero-Click Exploits Turned Smartphones into Silent Surveillance Tools
In 2019, cybersecurity researchers uncovered a spyware campaign so advanced that it redefined mobile threats. Pegasus, developed by the Israeli firm NSO Group, was designed not for mass financial theft but for covert surveillance. Unlike traditional malware that relies on phishing links or user interaction, Pegasus exploited critical vulnerabilities within messaging applications such as WhatsApp and iMessage to silently infiltrate smartphones.
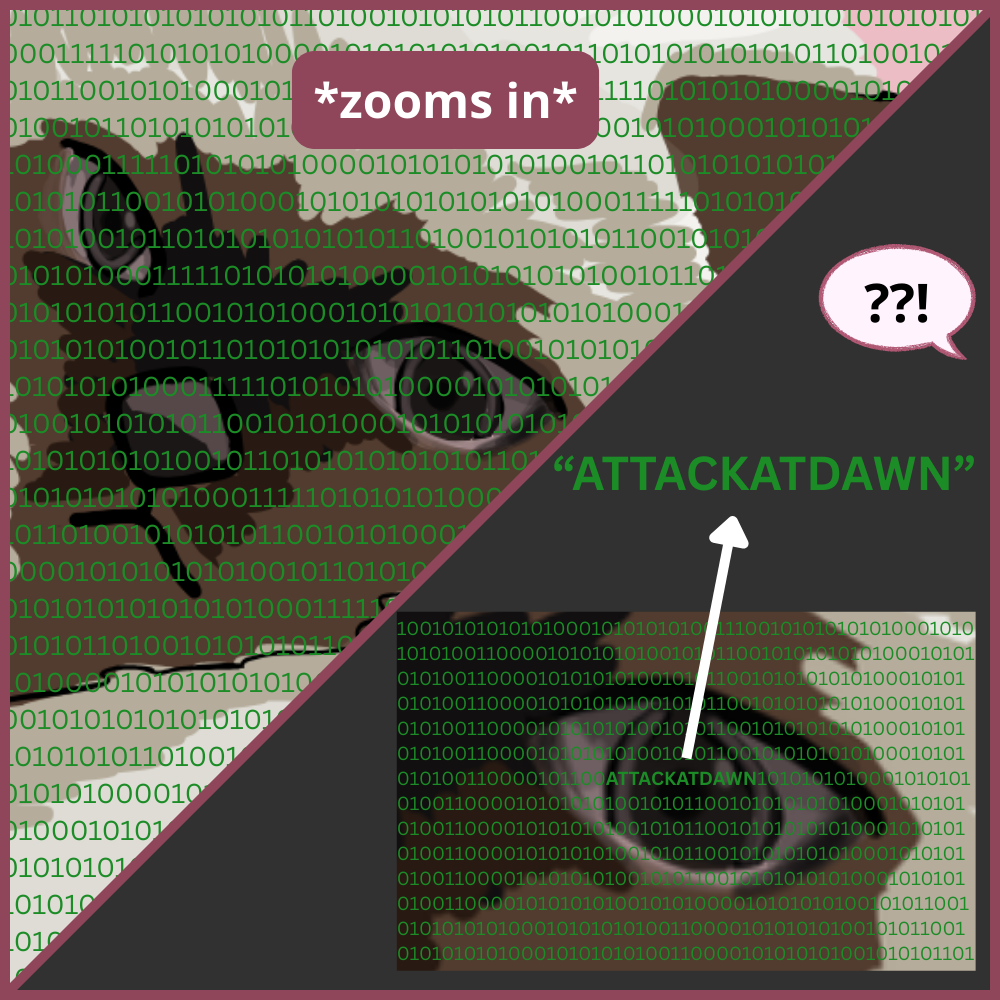
This malicious software leveraged zero-day vulnerabilities (previously unknown flaws in software), allowing Remote Code Execution (RCE) without requiring the victim to click or download anything. A specially crafted message would be automatically processed by the application, triggering the exploit chain. Once initial access was achieved, Pegasus escalated privileges, in some cases gaining root-level control over the device.
Furthermore, instead of breaking encryption during transmission, the spyware operated directly on the compromised device. Messages were captured after decryption, calls were recorded, and sensitive data was exfiltrated. The malware could activate the microphone and camera, access stored files, retrieve location data, and monitor communications — effectively turning a personal smartphone into a surveillance tool.
What made Pegasus particularly alarming was its precision. Reports indicated that journalists, activists, political figures, and government officials were among those allegedly targeted. This shifted the conversation from conventional cybercrime to state-level cyber operations and raised global concerns about privacy, digital rights, and the ethics of surveillance technology.
Upon discovery, companies such as Apple and WhatsApp issued security patches to close the exploited vulnerabilities, and forensic research methods were developed to detect traces of the spyware. However, the incident underscored a critical reality: even the most secure consumer devices are only as safe as their latest update.
The key takeaway is that modern cyber threats are no longer limited to stealing data for profit. When vulnerabilities remain unpatched, even a device in your pocket can become an invisible surveillance instrument. In cybersecurity, trust must be continuously verified because sometimes the threat does not knock before entering.