CVE-2017-5638 and the Breach That Followed
In May of 2017, one of the U.S.’s largest credit reporting agencies, Equifax, suffered a massive data breach
that is still discussed today due to how avoidable it was.
The breach began when attackers exploited a known vulnerability, CVE-2017-5638, which is a critical remote code
execution (RCE) vulnerability that allows attackers to run arbitrary commands on affected web servers. Equifax
failed to patch the vulnerability in time, allowing attackers to gain unauthorized access to its systems in
mid-May 2017.
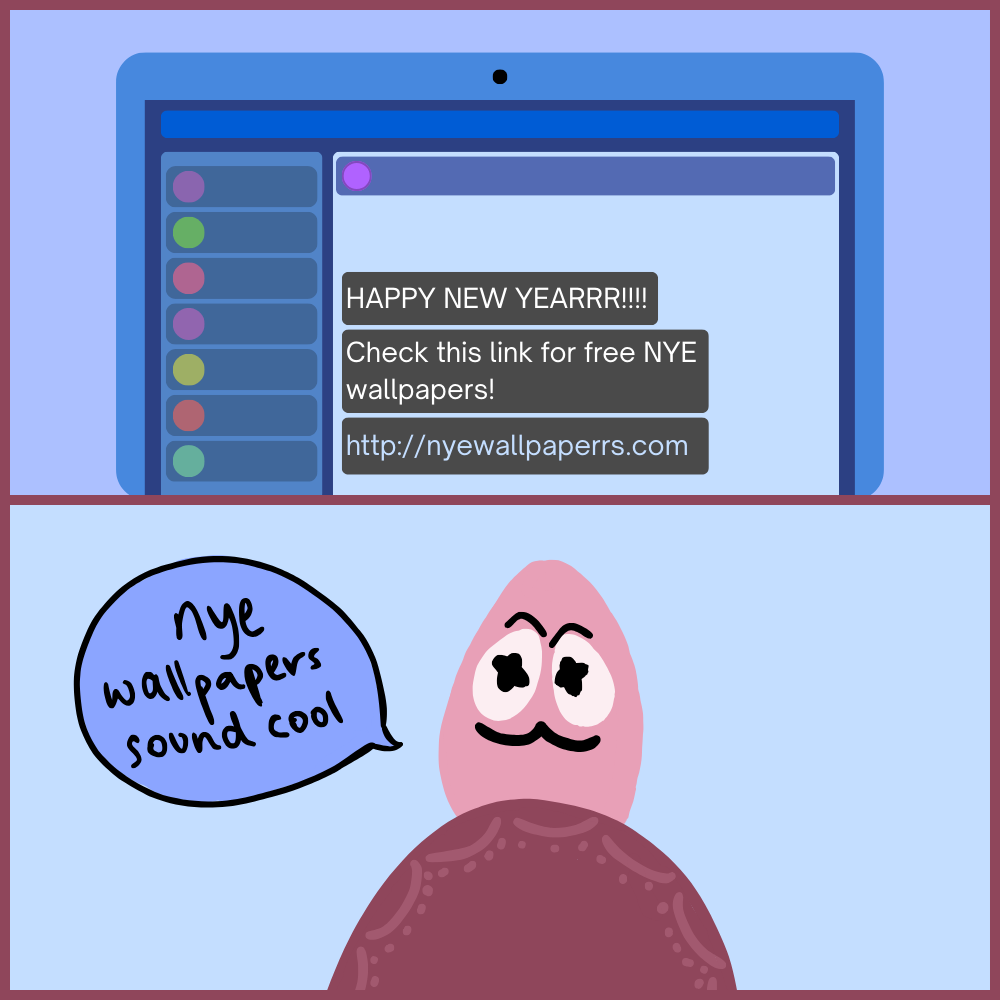
Over the next several weeks, the attackers dug their way to a goldmine of confidential records, containing the PII of
millions of individuals. This data was soon exfiltrated in small chunks to not alert the company and was also encrypted
in transmission. Usually, a company as big as Equifax would have detected this malicious act, but the attackers were in
luck; Equifax was using a traffic inspection tool that failed because the security certificate for that tool had expired,
and it could not detect this data.
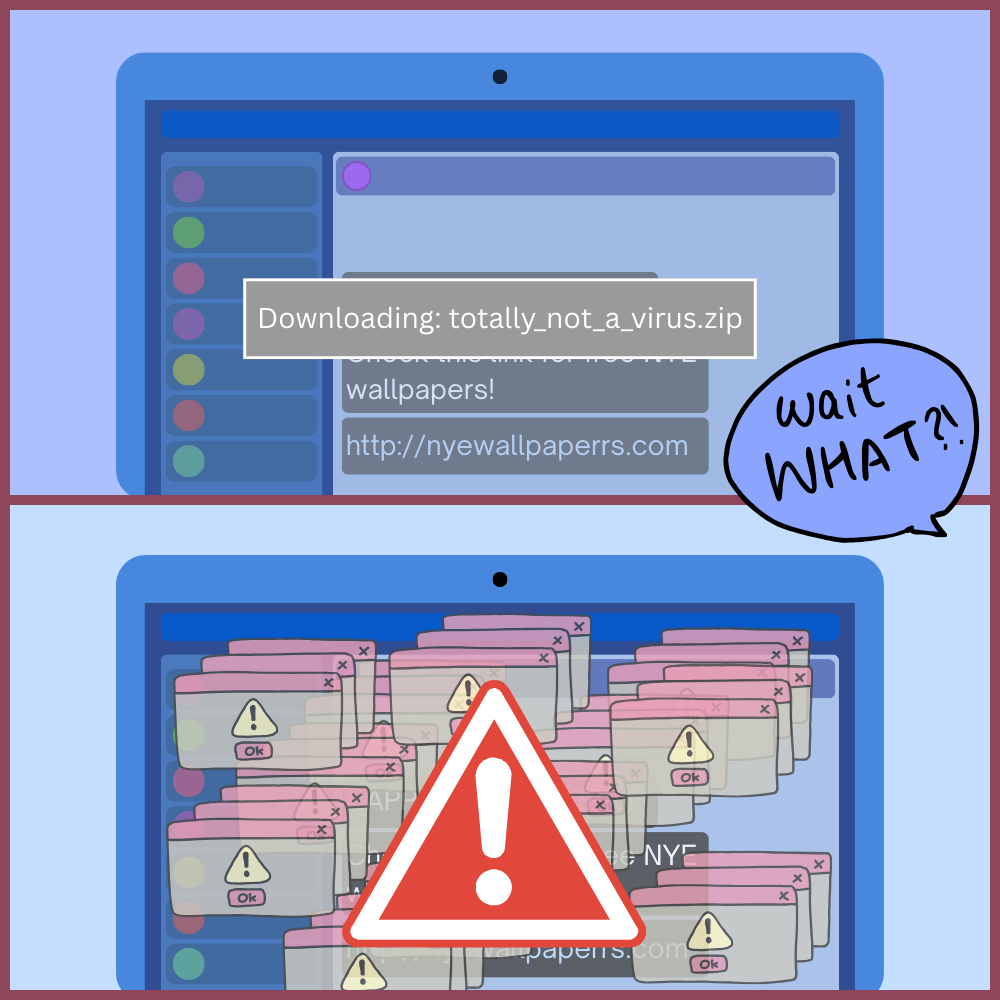
Later, in July, when the certificate was updated, the agency became aware of there being a malicious presence in their
systems and began investigating without informing the public. After a month, an official message was posted, and a website
for aiding the affected was created. Equifax faced a lot of backlash for this grave compromise of personal records and their
amateur way of dealing with this breach.
It was found that the attackers could have been from the Chinese military, of which 4 were indicted. While the stolen data was
never publicly dumped on the dark web, U.S. authorities believe the breach was conducted for intelligence-gathering purposes.
This incident highlights the importance of timely patching, frequent security audits, and maintaining up-to-date security controls
to prevent avoidable breaches.
The Price of Negligence: How Equifax Lost Trust
Equifax wasn’t hacked because attackers were brilliant — it was breached because basic cybersecurity discipline failed at a company
that controlled the financial identities of half a nation.
May-July 2017 was a devastating period for Equifax as a cyberattack resulted in the credit bureau being robbed of personal data of
147 million people. This personal data included social security numbers, addresses, license numbers, and credit card numbers. But what
struck worse was that providing these details was mandatory for consumers, meaning the attack affected those who were hesitant to
provide these details but were reassured by Equifax.
The attack has been estimated to cost Equifax about $1.4 Billion– law suits, regulatory fines, security remediation, and more. While this
$1.4 Billion was financially no issue, strategically it had caused the company to fall apart. Financially, the company was able to split
the costs over upcoming years and cancel out some of the balance with cyber insurance. Moreover, Equifax, in itself, is a large, profitable
firm with billions in annual revenue. On the other hand, the company faced serious reputational damage, becoming synonymous with negligence.
Furthermore, the regulatory board and US government, was no less than hostile as board-level accountability was questioned and cybersecurity
was reframed as fiduciary duty, not IT hygiene.
Several senior executives resigned or were fired. This was because the breach was a management failure, rather than an IT failure. The breach
is often described to be very preventable because nothing about it required advanced hacking or novel techniques, hence termed as an “oversight
failure”. Once public, regulatory and media scrutiny intensified, while insider-trading allegations further damaged leadership credibility.
Retaining the same executives would have signaled weak accountability. Their exit reflected a shift in cybersecurity from an operational issue to
a fiduciary responsibility at the board level.
This breach cost Equifax its credibility, not just its systems.